December 2021/January 2022 Release Notes
Administration
Automated Graduation
Following feedback from some client groups, we have relocated the Automated Idea Graduation setting. The aim is to provide more control of the challenge event lifecycle for innovation teams. There are often scenarios within the process where a "pause" is needed while ideas are evaluated. This update is focused on improving the user experience in that scenario.
Administrators now have access to the setting which can control the ability for ideas to graduate automatically. Previously, this setting was only available to Planview IdeaPlace Administrators. The setting is now available when accessing the Setup Settings menu within Administration.
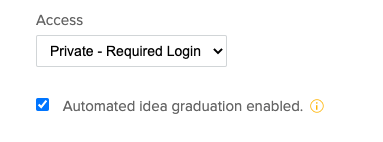
Figure 1 - Checkbox for enabling Automated Graduation
The setting is enabled by default, which means that the ideas automatically graduate according to the configuration that is set in the Graduation Thresholds section.
If this setting is disabled, idea graduation will cease to be automated. All settings configured in the Graduation Thresholds page will no longer result in ideas being graduated. When turned back on (from the disabled state), idea graduation will resume.
User Experience – View Ideas
Increased Idea Number Displayed
When a user accesses the View Ideas page, the default number of ideas that will be displayed has been increased to 27. Previously, it was a setting that capped the display to 9 ideas. This setting update is applied across the instance and will be the same in all challenge events.
Comparable Ideas
Commenting from Lightbox
Following reports of an issue relating to idea commenting through Comparable Ideas, we have investigated and published a fix for the issue.
When accessing an idea using the Comparable Ideas tab, an issue was reporting with regards to commenting on the Comparable Idea via the idea lightbox. Any user that navigated to an idea in the Comparable Ideas tab, then closed the idea before opening another Comparable Idea would see any comment posted be visible on the previous idea they accessed.
The behavior has been corrected. Comments posted via the idea lightbox (accessed through Comparable Ideas) will now be published to the correct idea.
Security
Log4J Upgrades
- Following the release of version 2.17.1, we upgraded to use this version. This removes the vulnerability of a remote code execution attack whereby the attacker (with permission) modifies the logging configuration file. This can be used to construct a malicious configuration using a JDBC appender, which allows the data source to be used to execute a remote code. This issue is fixed by limiting the JNDI data source names to the Java protocol in Log4j2 versions 2.17.1, 2.12.4, and 2.3.2
- Following the release of version 2.17.0, we upgraded to use this version. This version adds protection from uncontrolled recursion from self-referential lookups. This allowed an attacker with control over Thread Context Map data to cause a denial of service when a crafted string is interpreted. This issue was fixed in Log4j 2.17.0
- Following the release of version 2.16.0, we upgraded to v2.16.0. This version removes the JNDI classes from Log4J.
Log4J Vulnerability
Following the public reporting of a vulnerability for certain versions of Log4j2, we have upgraded our version to v2.15.0. This remediates a transitive vulnerability on version 2.11.2.
This has been regression tested and confirmed to be working. This remediation was shipped on Wednesday, 15 December 2021. Furthermore, we have reviewed and made necessary changes to the 2.15.0 configuration and determined that current issues impacting 2.15.0 do not apply to our IdeaPlace configuration.
The IdeaPlace application will upgrade to v2.16.0 (or the current available release) in the weekly upgrade on Wednesday, 22 December 2021. Updates will be provided as the situation develops.
HMTL Code Injection
Following the identification of an issue relating to the ability to inject HTML code via the user registration page, we have taken action to prevent this.
During a penetration test, a scenario was identified whereby the user registration fields could be used to inject HTML code. Specifically, this relates to the first and last names on the standard registration page.
This has been updated so that any attempt to insert HTML code will trigger the following errors to the user:
First Name contains illegal characters. Access Denied.
Last Name contains illegal characters. Access Denied.

